Flooding the online scammers in a sea of leads
Online scammers are sending emails with contact forms to collect potential victims. I thought I'd let them work for it.
Every few weeks, a scammer sends a contact form submission to one of our company’s websites. The message is always the same shape: an inquiry that sounds almost legitimate, a callback number that goes somewhere in Southeast Asia, and an email address that exists only long enough to harvest replies.
They’re using automated tools to fill our forms. I thought I’d return the favour.
What the tool does
It generates fictional people. Each one gets a randomly assembled English name and a plausible email address. Then it submits them, one by one, to a target contact form — paced to look like organic traffic. More submissions during business hours, fewer at night. Each request comes from a different browser user agent string.
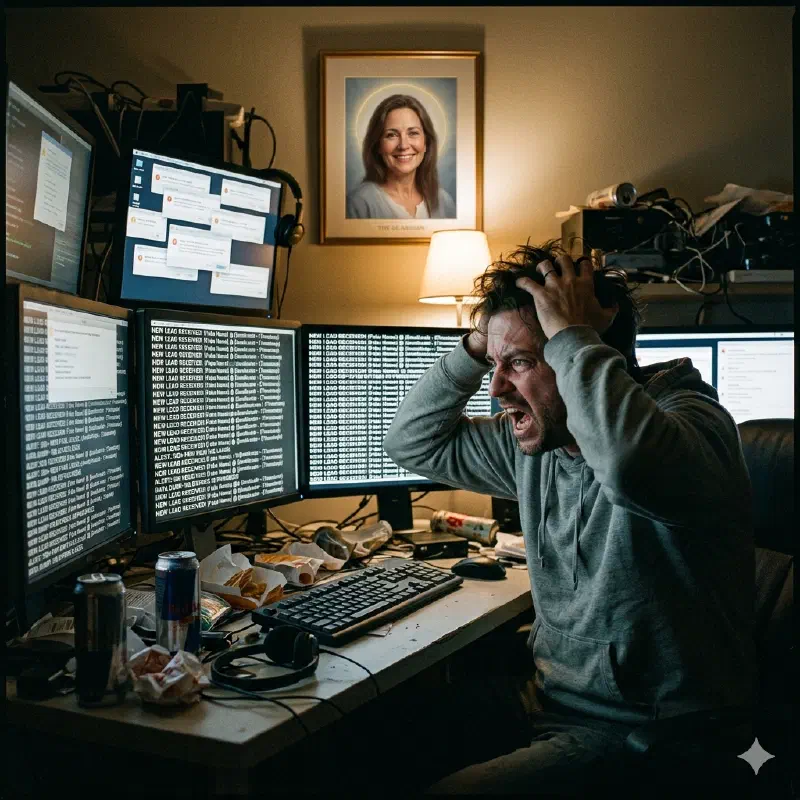
The result is a contact list full of people who don’t exist, with email addresses that bounce. A scammer’s sales funnel, quietly filled with noise.
The code is about 130 lines of Go. It reads a JSON file with first names, last names, and email domains, and does the rest with the standard library.
Why Go
It was a good excuse. The concurrency model is overkill for a sequential script, but the HTTP client and encoding packages are clean and the binary compiles to a single file with no runtime dependencies. Convenient for something you might want to run on a cheap VPS.
The ethical footnote
Using this on any website you don’t own is a bad idea and likely illegal in your jurisdiction regardless of how much you dislike the recipient. The Finnish computer crimes act doesn’t include a “but they were scammers” exception, and neither does any other law I’m aware of.
The code is on GitHub. It’s framed as a form load tester, which is the only legal use for it. The scammer application is left as an exercise for the reader’s conscience.
